BOOK THIS SPACE FOR AD
ARTICLE ADExclusive Threatpost research examines organizations’ top cloud security concerns, attitudes towards zero-trust and DevSecOps.
Over the past 15 years, the cloud has blown business into a new age of networking, for solid reasons: Small businesses can get online fast, using the same tools as the big companies; large companies can scale up and down to match demand; and organizations of all sizes can quickly react to business fluctuations in terms of allocating resources and onboarding applications.
As well, of course, over the past few years, the pandemic has made cloud resources crucial when it comes to supporting remote workforces.
[Editor’s Note: This article was originally published in the free Threatpost eBook “Cloud Security: The Forecast for 2022.” In it we explore organizations’ top risks and challenges, best practices for defense, and advice for security success in such a dynamic computing environment, including handy checklists. Please download the FREE eBook for the full story]
However, the mad dash to set up shop in the cloud can sometimes lead to stormy weather: There are, after all, beaucoup security challenges hidden behind the cloud’s promise of blue skies. As Prevailion CTO Nate Warfield enumerates, cloud marketplaces “are rife with pre-built virtual machine (VM) images containing unpatched vulnerabilities, overly permissive firewall settings, and even malware and coin miners. Cloud providers don’t take a proactive stance towards breach and compromise monitoring and, in many cases, won’t even pass on notifications to their customers which they have received from external researchers.”
In order to put some quantifiable numbers around how organizations are faring in their journeys to the cloud, Threatpost polled 400+ readers. Topics included what security dangers respondents have encountered, and which ones they most fear they’ll run into. We also asked what security tools they plan to implement in the coming months.
When asked how confident respondents are that their organization had implemented sufficient cloud security, the majority felt bullish (68 percent). Worryingly, almost a quarter (24 percent) said they had no confidence in their organization’s cloud security. Just 8 percent said they feel “highly” confident.
Lions & Tigers & Shared
Responsibility
Warfield’s list of challenges is just the tip of the iceberg, according to the poll results. There are also data-privacy and regulatory issues; the basic challenges of implementing cloud, such as staff shortages; the threat of cyberattack and data exposure; and plain old confusion.
Not everyone is sure who’s responsible for what when it comes to the sharedresponsibility model for public cloud deployments. And, a recurring question is what zero-access architecture for access management entails.
Just over half said they have embraced the shared-responsibility model for public cloud deployments (59 percent), but a quarter said they “don’t really understand it” and 12 percent said they did not. When asked if they’ve implemented a zero-trust architecture for access management, 53 percent said, “not yet but plan to,” and 17 percent said it confused them. Just 23 percent said yes. Six percent said absolutely not.
The notion of “DevSecOps,” where security is built into an organization’s cloudnative application lifecycle management, has more support: 71 percent noted that they’ve either adopted the strategy or soon plan to; but a fifth (21 percent) said they didn’t fully grasp what it means.
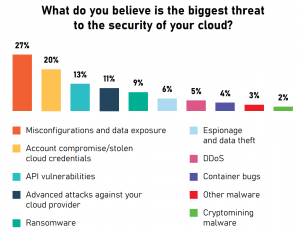
Meanwhile, organizations perceive there to be a lot of security pitfalls in the cloud. In its poll, Threatpost asked about a number of them, from API vulnerabilities to stolen cloud credentials, and container bugs to a smorgasbord of malware, including ransomware and cryptomining malware.
Security Pitfall No. 1: Misconfigurations
The biggest number of respondents – 27 percent – cited misconfigurations and data exposure as the biggest threat to their cloud deployments.
While many respondents reported that they’ve either experienced a cyberattack on their cloud assets in the past 12 months (18 percent) or that they aren’t exactly sure (2 percent), an even larger portion – 38 percent – reported having experienced a data-exposure incident due to misconfiguration.
Poll respondents’ takes on the issues confirm what’s been a constant over the past few years; namely, misconfigured cloud deployments have been, and continue to be, rampant. In a 2020 survey of 2,064 Google Cloud buckets by Comparitech, 6 percent of all Google Cloud buckets were estimated to be misconfigured and left open to the public internet, for anyone to access their highly sensitive content.
Respondents ranked their other most-worrying cloud security threats as account compromise and stolen cloud credentials, (20 percent); API vulnerabilities (13 percent); advanced attacks against cloud providers (11 percent); ransomware (9 percent); cyberespionage/data theft (6 percent); distributed denial of service (DDoS, 5 percent); other malware (3 percent); and cryptojacking (2 percent).
How You’re Protecting the Cloud
Fortunately, efforts to secure the cloud aren’t static. Nor are the technologies. When asked what security tools they’re planning on implementing in the next 12 months, poll respondents listed a host of technologies that will hopefully fill in whatever holes they have in their cybersecurity umbrellas.
For better or worse, multifactor authentication (MFA) on all accounts was cited as the top tool already in use by the most respondents, at 12 percent. It’s important however not to fall into a false sense of security: In January 2021, the feds warned that cloud attacks were bypassing weaker two-factor authentication, such as schemes that use a code sent to a mobile phone via SMS.
In terms of the top security tools that poll respondents plan to invest in, encryption for data at rest and data in transit (cited by 11 percent) took the lead, followed by identity access management (11 percent) and the adoption of self-managed security controls offered by cloud providers (9 percent).
The top most-cited planned upgrade to cloud security in the poll was user-behavior analytics: i.e., the use of artificial intelligence and machine learning to analyze large datasets and identify patterns that signify security breaches. This can be used to spot anomalous behavior that may indicate data exfiltration or other malicious activity that might otherwise slip by security tools and personnel. In all, 9 percent of respondents said their organizations have behavior analytics in the works in the coming year.
The next set of top cloud-security tools on the to-do list were cloudconfiguration monitoring tools (cited by 8 percent), a single console to manage security across multiple clouds (7.5 percent), and MFA on all accounts (7.5 percent). Next up were risk assessment and auditing (7.5 percent), policybased data loss prevention (DLP) (7 percent) and data activity monitoring (7 percent).
What’s Gumming Up the Works
Some security tools are in place, while more are being implemented. But all of this work to secure the cloud is, well, work, and it often requires more hands than are available. As noted earlier, respondents cited a lack of skilled staff as the biggest challenge when it comes to securing the cloud, (19 percent).
Indeed, the (ISC)²’s 2021 Cybersecurity Workforce Study found that there are 2.72 million open cybersecurity positions globally, and that the worldwide cybersecurity workforce needs to grow 65 percent to effectively defend organizations’ critical assets. Out of those, cloud management and cybersecurity ranked highest when it comes to the biggest talent gaps that companies need to fill.
The next biggest challenge facing organizations is a lack of visibility into what data is held within cloud applications, cited by 13 percent. That’s followed by insufficient identity and access management controls at 11 percent.
It’s clear that cloud security is increasingly top-of-mind at organizations, which have big plans for addressing it. But it’s a proverbial journey, not a sprint. As Prevailion’s Warfield noted, it’s crucial to take it seriously, and the time is now to start implementing controls.
“Cloud networking isn’t inherently insecure,” he said. “But as the world shifts to a cloud-centric and hybrid cloud environment, particularly for remote workforces, organizations need to recognize that their cloud-security strategy, policies, controls and processes must be as robust as in a classic onpremises environment.”
Moving to the cloud? Discover emerging cloud-security threats along with solid advice for how to defend your assets with our FREE downloadable eBook, “Cloud Security: The Forecast for 2022.” We explore organizations’ top risks and challenges, best practices for defense, and advice for security success in such a dynamic computing environment, including handy checklists.
.png)



















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·