BOOK THIS SPACE FOR AD
ARTICLE AD17. January 2022
This article has been indexed from
CySecurity News – Latest Information Security and Hacking Incidents
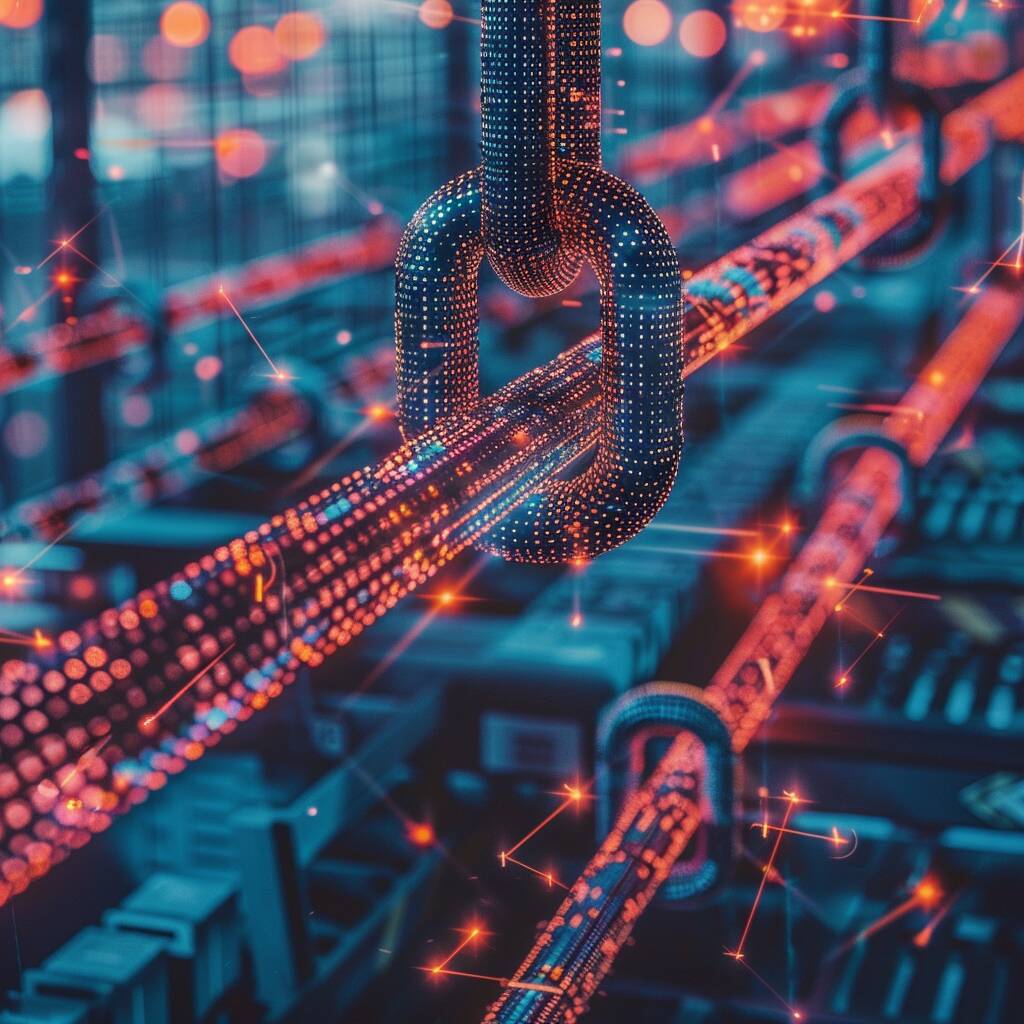
ESET researchers investigated the misuse of vulnerable kernel drivers in depth saying “Software” drivers are among the different types of kernel drivers that provide particular, non-hardware-related capabilities such as software debugging and diagnostics, as well as system analysis. These have the potential to greatly increase the attack surface.
Although it is no longer possible to directly load a malicious, unsigned driver in current versions of Windows, and kernel rootkits are deemed obsolete, there are still ways to load malicious code into the kernel, particularly through manipulating legal, signed drivers. There are many drivers available from a variety of hardware and software suppliers that allow you to completely access the kernel with minimal effort.
The most common vulnerabilities detected in-kernel drivers:
“When malware actors need to run malicious code in the Windows kernel on x64 systems with driver signature enforcement in place, carrying a vulnerable signed kernel driver seems to be a viable option for doing so,” says Peter Kálnai, Senior Malware Res
[…]
Content was cut in order to protect the source.Please visit the source for the rest of the article.
Read the original article:
By continuing to use the site, you agree to the use of cookies. more information
.png)












 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·