BOOK THIS SPACE FOR AD
ARTICLE AD
A vulnerability in Verizon's Call Filter feature allowed customers to access the incoming call logs for another Verizon Wireless number through an unsecured API request.
The flaw was discovered by security researcher Evan Connelly on February 22, 2025, and was fixed by Verizon sometime in the following month. However, the total period of exposure is unknown.
Verizon's Call Filter app is a free utility that offers users spam detection and automatic call blocking. A paid version (Plus) adds a spam lookup and risk meter, the ability to apply blocks by type of caller, and receive caller ID on unknown numbers.
The free version of the app comes pre-installed and enabled by default on eligible Android and iOS devices bought directly from Verizon, and is believed to be used on millions of devices.
Connelly told BleepingComputer that he only tested the iOS app. However, he noted that the Android app was also very likely impacted by the same bug, as the issue was with the feature's API rather than the apps themselves.
Exposing call histories
When using the Call Filter app, Connelly discovered that the app would connect to an API endpoint, https://clr-aqx.cequintvzwecid.com/clr/callLogRetrieval, to retrieve the logged-in user's incoming call history and display it in the app.
"This endpoint requires a JWT (JSON Web Token) in the Authorization header using the Bearer scheme and uses an X-Ceq-MDN header to specify a cell phone number to retrieve call history logs for," explains Connelly.
"A JWT has three parts: header, payload, and signature. It's often used for authentication and authorization in web apps."
Connelly says the payload includes various data, including the phone number of the logged-in user making the request to the API.
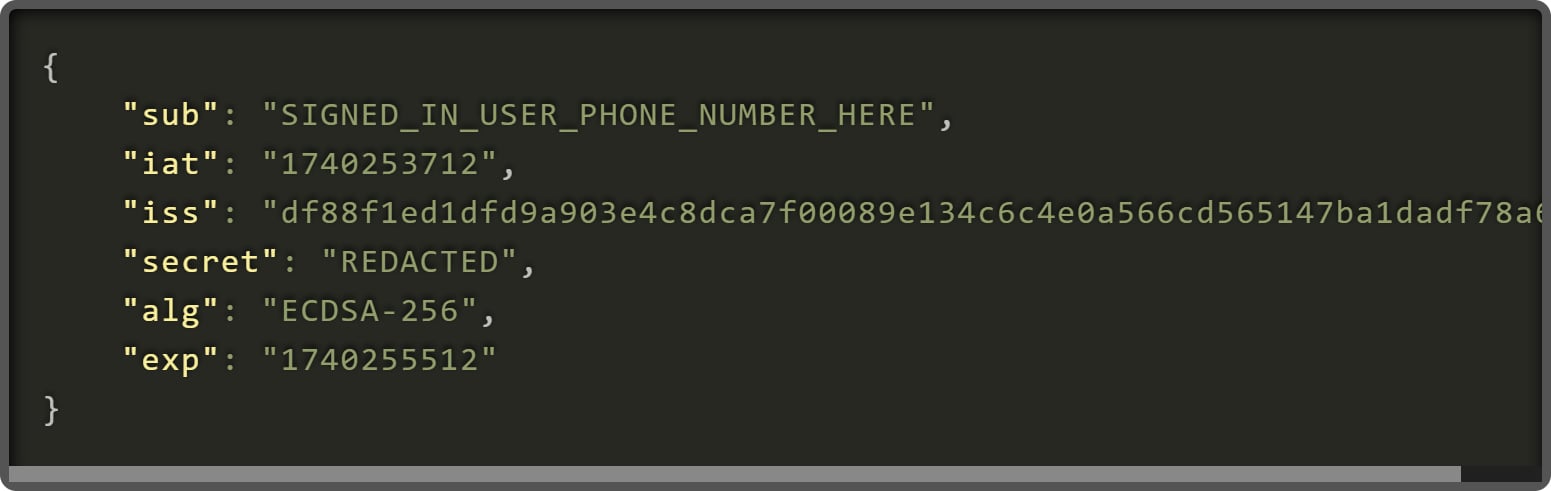 JWT payload
JWT payloadSource: Connelly
However, the researcher discovered that the phone number in the JWT payload for the logged-in user was not verified against the phone number whose incoming call logs were being requested.
As a result, any user could send requests using their own valid JWT token, but replace the X-Ceq-MDN header value with another Verizon phone to retrieve their incoming call history.
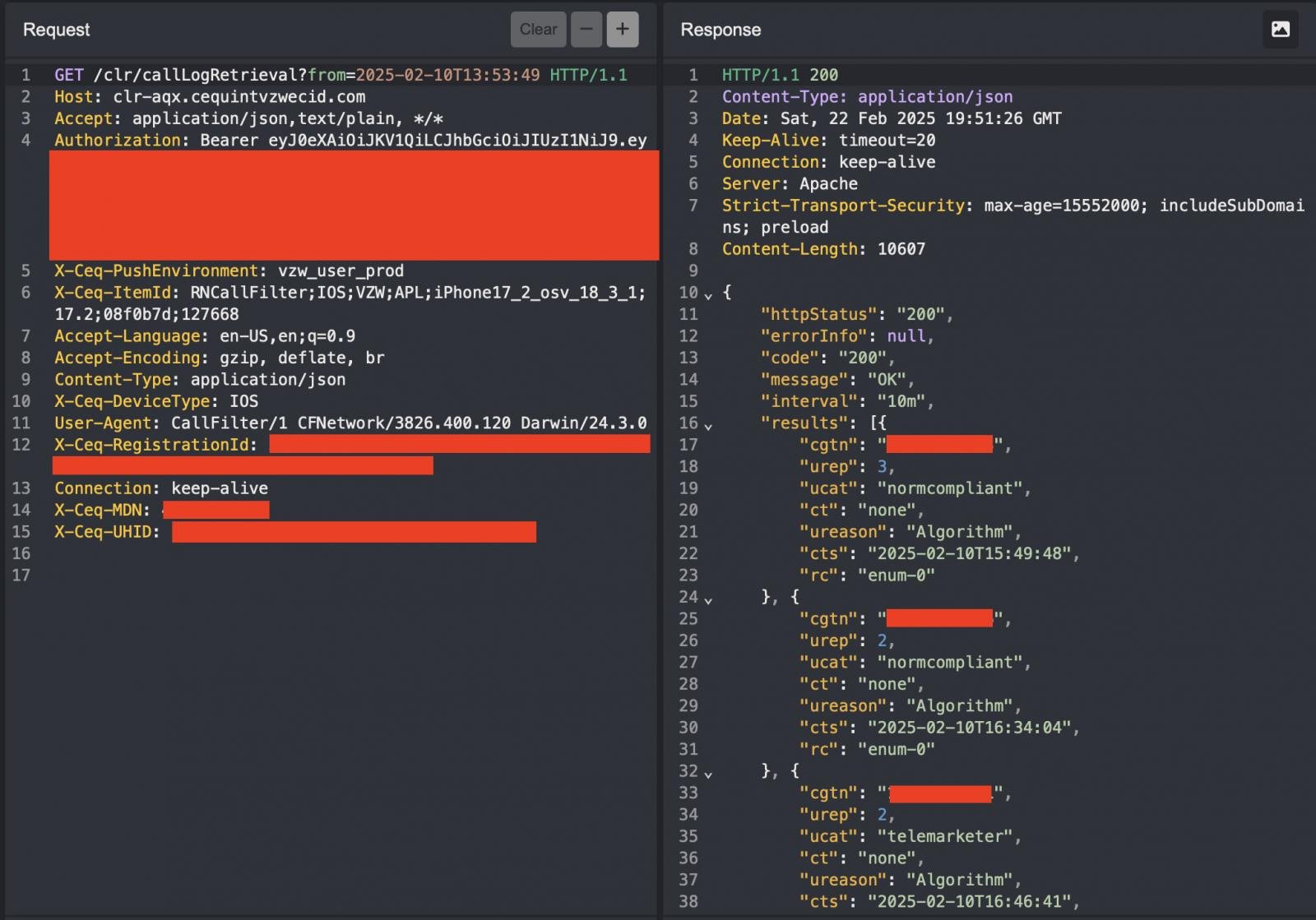 Example request sent to the vulnerable API
Example request sent to the vulnerable APISource: evanconnelly.github.io
This flaw is particularly sensitive for high-value targets like politicians, journalists, and law enforcement agents, as their sources, contacts, and daily routines could be mapped out.
"Call metadata might seem harmless, but in the wrong hands, it becomes a powerful surveillance tool. With unrestricted access to another user's call history, an attacker could reconstruct daily routines, identify frequent contacts, and infer personal relationships," explained Connelly.
It is unclear if rate limiting was in place to prevent mass scraping for millions of subscribers, but Connolly told BleepingComputer he saw no indication of such a mechanism or an API gateway that usually implements a security feature like this.
Poor security practices
Although the researcher commends Verizon for its prompt response to his disclosure, he highlighted worrying practices the telecom firm has followed in handling subscribers' call data.
The vulnerable API endpoint used by Call Filter appears to be hosted on a server owned by a separate telecommunications technology firm called Cequint, which specializes in caller identification services.
Cequint's own website is offline, and public information about them is limited, raising concerns about how sensitive Verizon call data is handled.
BleepingComputer contacted Verizon to ask when the flaw was introduced, if it was seen exploited in the past, and if it impacted all Call Filter users but has not received a response at this time.
.png)















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·