Authz0 is an automated authorization test tool. Unauthorized access can be identified based on URLs and Roles & Credentials.
URLs and Roles are managed as YAML-based templates, which can be automatically created and added through authz0. You can also test based on multiple authentication headers and cookies with a template file created/generated once.
Key Features Generate scan template $ authz0 new Include URLs Include Roles Include ZAP history (Select URLS > Save Selected Entiries as HAR) Include Burp history (Select URLs > Save item) Include HAR file Easy modify scan template (Role, URL) $ authz0 setUrl $ authz0 setRole authz0 setCred Scanning authorization(access-control) with template $ authz0 scan
Installationgo install
homebrew
brew install authz0
Need more information? please refer to installation guide
UsageAvailable Commands:
help Help about any command
new Generate new template
scan Scanning
setCred Append Credential to Template
setRole Append Role to Template
setUrl Append URL to Template
version Show version
1. Generate template
e.g
authz0 new target.yaml --include-zap zapurls.har
authz0 new target.yaml --include-burp burpurl.xml
2. Modify template
authz0 setRole <filename> [flags]
authz0 setUrl <filename> [flags]
e.g
authz0 setRole target.yaml -n User1
authz0 setCred target.yaml -n User1 -H "X-API-Key: 1234" -H "TestHeader: 12344"
3. Scanning
e.g
authz0 scan target.yaml -r TestUser1 -H "Cookie: 1234=1234" -H "X-API-Key: 1234555"
DocumentsQuestion
Please use discussions actively!
ChangelogDetailed changes for each release are documented in the release notes.
Contributing
Authz0's open-source project and made it with
if you want contribute this project, please see CONTRIBUTING.md and Pull-Request with cool your contents.
.png)
 2 years ago
104
2 years ago
104 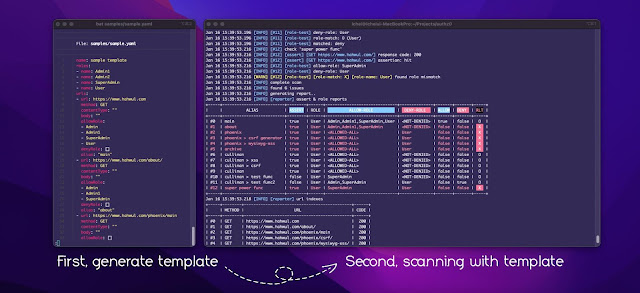
















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·