AutoResponder is a tool aimed to help people to carry out their Incident Response tasks WITH the help of Carbon Black Response's awesome capabilities and WITHOUT much bothering IT/System/Network Teams
| Delete Files | ✔️ |
| Delete Registry Values | ✔️ |
| Delete Win32 Service Entries | ✔️ |
| Delete Scheduled Task Entries | ✔️ |
| Detailed Sensor List Export | ✔️ |
| Find Files | ✔️ |
| Find Registry Values | ✔️ |
| Download Files | ✔️ |
| Download A list of Win32 Service Entries | ✔️ |
| Download A list of Scheduled Task Entries | ✔️ |
| Download A list of WMI Entries | ✔️ |
| Isolate/Unisolate Sensors | ✔️ |
| Kill Running Processes | ✔️ |
| Restart Sensors | ✔️ |
| Restart Endpoints | ✔️ |
| Generate CSV reports | ✔️ |
| Scan Collected binaries with THOR APT Scanner | ✔️ |
| Delete WMI Entries | ❌ |
| Solve the whole case and generate a nice report so we can all have a cold beer | ❌ |
| Government agency | ✔️ |
| State agency | ✔️ |
| Bank | ✔️ |
| Public/Private Institution | ✔️ |
| Company that has Carbon Black Response installed in the environment as an EDR product | ✔️ |
| A company doing Incident Response | ✔️ |
| Startup? (Doubt it) | ✔️ |
| Person who has no idea what Carbon Black is | ❌ |
For those who aren't familiar with Carbon Black Response, it is a quite amazing product that delivers a solution to Incident Response cases in its own unique and awesome way. Carbon Black Response has a python API integration which helps people automate their tasks - saving a lot of time. So all you see in this project is just python API magic - nothing more, nothing less.
For the past months there was a lot of Incident Response cases that our team had to deal with. Although we got through it like a champ, I've noticed that our team had been struggling to communicate with the customer's IT/System/Network Teams and when they did a single file search would result in weeks. Because we are Carbon Black's Incident Response partner and because we heavily use Carbon Black Response in most cases we're involved, I've decided to write a tool to help our team to get very BIG tasks done in a very short time with a minimum amount of help from others.
Fair enough, Now, Imagine a scenario where hundreds of the endpoints have been compromised, the attacker has established persistence on all of them and dropped a ton of files. And what a coincidence that is - whole IT team decided to go on a vacation leaving nobody back at the office to deal with the Incident and Domain Admin wants to file a paper for every key that's pressed on his keyboard - eleminating your ability to identify and eradicate threats on compromised systems. Good luck! (True story btw)
The code is written in python3 so any version above 3.4 will do fine
Download the zip archive or do a git clone Install required modules with pip3 install -r requirements.txt Configure Carbon Black API => https://cbapi.readthedocs.io/en/latest/ Kick assTo scan the binary repository with THOR you just need to
Obtain the thor linux package Add the valid license (Trial License is not supported) Upload the THOR directory to the CBR server you'd like to scan (Master on a single and Minion on a clustered environment) Run the run-thor moduleSpecial Thanks to
Big thanks to https://twitter.com/harunglec for helping out with the multi-threading module.
You can scan the whole binary repository containing executable files collected by CBR with THOR APT Scanner. https://twitter.com/thor_scanner
This is just a python code - which means feel free to modify it for your needs. Please report any issues to => https://github.com/lawiet47/autoresponder/issues
Current modules all have been tested against sensors that have Windows as an OS environment. But you can give it a try on linux too.
.png)
 2 years ago
161
2 years ago
161 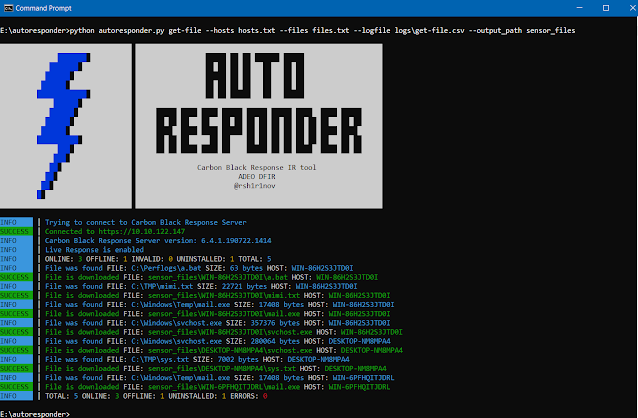
















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·