BOOK THIS SPACE FOR AD
ARTICLE AD
A new ransomware gang known as LockFile encrypts Windows domains after hacking into Microsoft Exchange servers using the recently disclosed ProxyShell vulnerabilities.
ProxyShell is the name of an attack consisting of three chained Microsoft Exchange vulnerabilities that result in unauthenticated, remote code execution.
The three vulnerabilities were discovered by Devcore Principal Security Researcher Orange Tsai, who chained them together to take over a Microsoft Exchange server in April's Pwn2Own 2021 hacking contest.
CVE-2021-34473 - Pre-auth Path Confusion leads to ACL Bypass (Patched in April by KB5001779) CVE-2021-34523 - Elevation of Privilege on Exchange PowerShell Backend (Patched in April by KB5001779) CVE-2021-31207 - Post-auth Arbitrary-File-Write leads to RCE (Patched in May by KB5003435)While Microsoft fully patched these vulnerabilities in May 2021, more technical details were recently disclosed, allowing security researchers and threat actors to reproduce the exploit.
As reported last week by BleepingComputer, this has led to threat actors actively scanning for and hacking Microsoft Exchange servers using the ProxyShell vulnerabilities.
After exploiting an Exchange server, the threat actors dropped web shells that could be used to upload other programs and execute them.
At the time, NCC Group's vulnerability researcher Rich Warren told BleepingComputer that the web shells were being used to install a .NET backdoor that was downloading a harmless payload at the time.
Since then, security researcher Kevin Beaumont reports that a new ransomware operation known as LockFile uses the Microsoft Exchange ProxyShell and the Windows PetitPotam vulnerabilities to take over Windows domains and encrypt devices.
When breaching a network, the threat actors will first access the on-premise Microsoft Exchange server using the ProxyShell vulnerabilities. Once they gain a foothold, Symantec says the LockFile gang uses the PetitPotam vulnerability to take over a domain controller, and thus the Windows domain.
From there, it is trivial to deploy the ransomware through the entire network.
What we know about the LockFile ransomware
At this time, there is not much known about the new LockFile ransomware operation.
When first seen in July, the ransom note was named 'LOCKFILE-README.hta' but did not have any particular branding, as shown below.
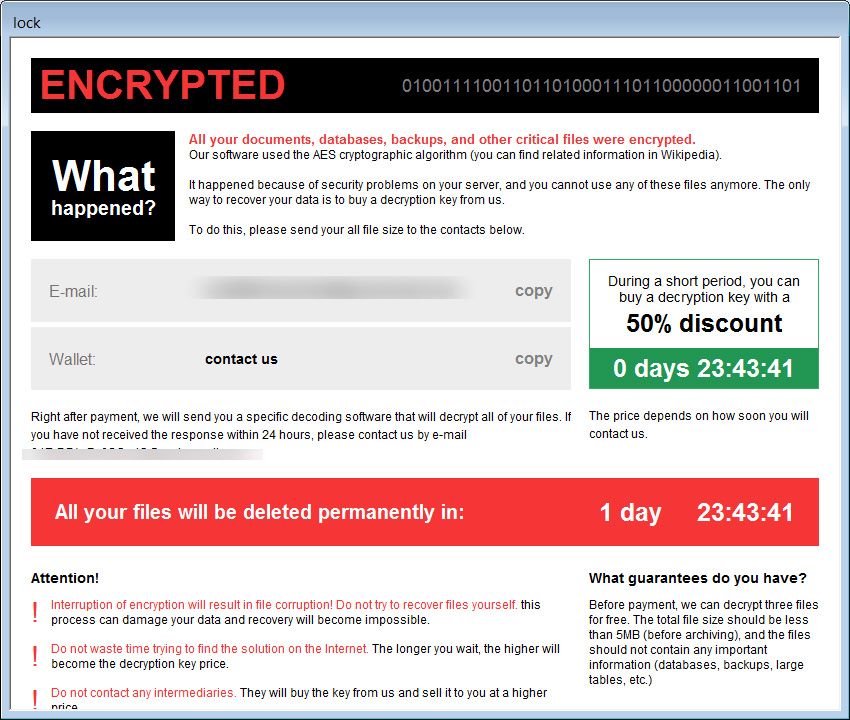 Old LockFile ransom notes
Old LockFile ransom notesStarting last week, BleepingComputer began receiving reports of a ransomware gang using branded ransom notes indicating that they were called 'LockFile,' as shown below
These ransom notes use a naming format of '[victim_name]-LOCKFILE-README.hta' and prompted the victim to contact them via Tox or email to negotiate the ransom. The current email address used by the operation is contact@contipauper.com, which appears to be a reference to the Conti ransomware operation.
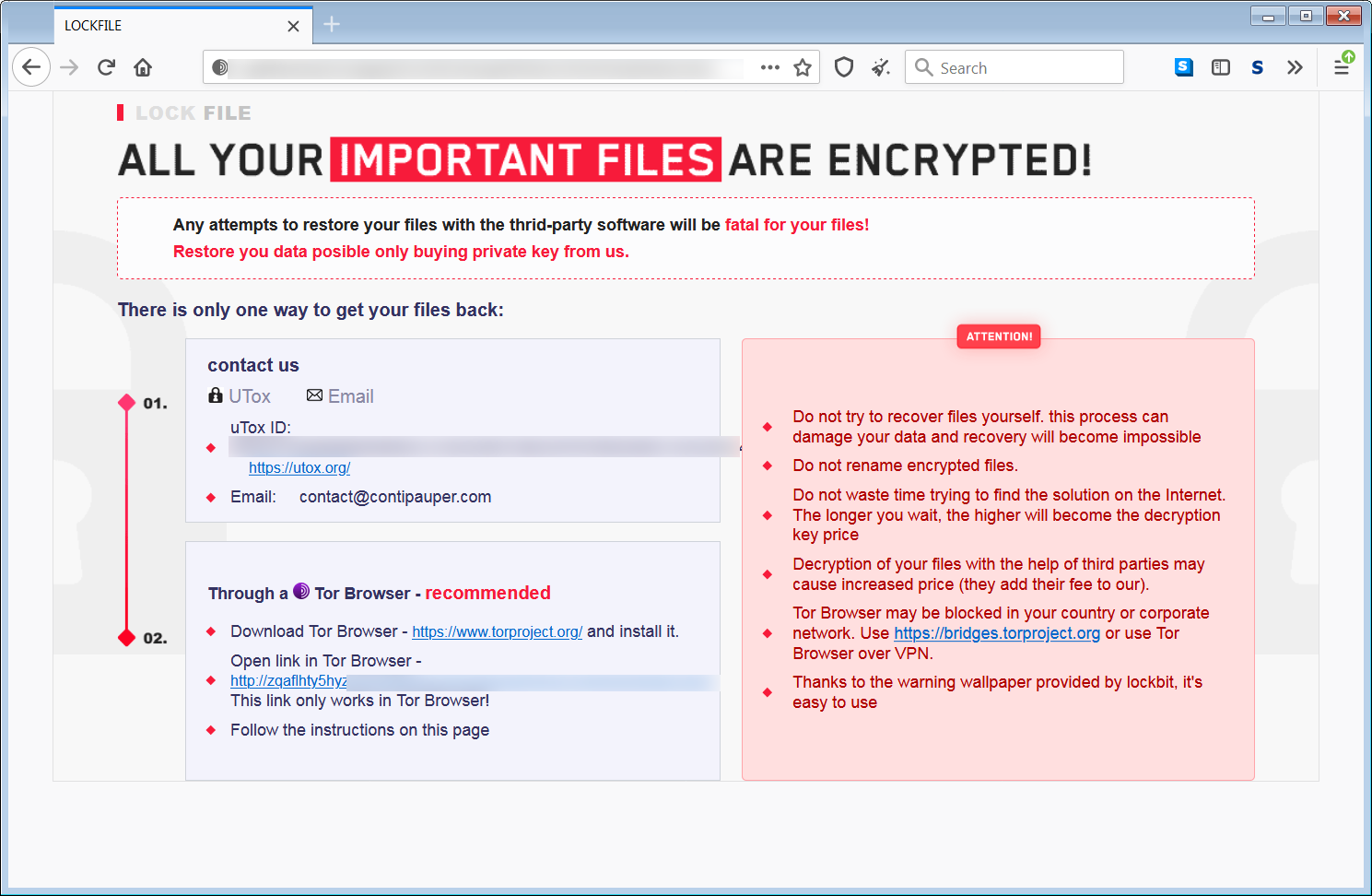
While the color schemes of the ransom notes are similar, the communication methods and wording make it unclear if they are the same operation.
Of particular interest is that the color scheme and layout of the ransom notes is very similar to the LockBit ransomware, but there does not appear to be any relation.
When encrypting files, the ransomware will append the .lockfile extension to the encrypted file's names.
Yesterday afternoon, when BleepingComputer and ransomware expert Michael Gillespie analyzed the July version of LockFile, we found it to be a noisy ransomware, taking up many system resources and causing temporary freezes of the computer.
Patch now!
As the LockFile operation uses both the Microsoft Exchange ProxyShell vulnerabilities and the Windows PetitPotam NTLM Relay vulnerability, it is imperative that Windows administrators install the latest updates.
For the ProxyShell vulnerabilities, you can install the latest Microsoft Exchange cumulative updates to patch the vulnerabilities.
The Windows PetitPotam attack gets a bit complicated as Microsoft's security update is incomplete and does not patch all the vulnerability vectors.
To patch the PetitPotam attack, you can use an unofficial patch from 0patch to block this NTLM relay attack vector or apply NETSH RPC filters that block access to vulnerable functions in the MS-EFSRPC API.
Beaumont says you can perform the following Azure Sentinel queries to check if your Microsoft Exchange server has been scanned for the ProxyShell vulnerability.
W3CIISLog | where csUriStem == "/autodiscover/autodiscover.json" | where csUriQuery has "PowerShell" | where csMethod == "POST"All organizations are strongly advised to apply the patches as soon as possible and create offline backups of their Exchange servers.
.png)















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·