BOOK THIS SPACE FOR AD
ARTICLE AD
A new Android banking malware named 'DroidBot' attempts to steal credentials for over 77 cryptocurrency exchanges and banking apps in the UK, Italy, France, Spain, and Portugal.
According to Cleafy researchers who discovered the new Android malware, DroidBot has been active since June 2024 and operates as a malware-as-a-service (MaaS) platform, selling the tool for $3,000/month.
At least 17 affiliate groups have been identified using malware builders to customize their payloads for specific targets.
Although DroidBot lacks any novel or sophisticated features, analysis of one of its botnets revealed 776 unique infections across the UK, Italy, France, Turkey, and Germany, indicating a significant activity.
Also, Cleafy says the malware appears to be under heavy development at the time, with signs of attempting expansion to new regions, including Latin America.
The DroidBot MaaS operation
DroidBot's developers, who appear to be Turkish, provide affiliates with all the tools required to conduct attacks. This includes the malware builder, command and control (C2) servers, and a central administration panel from which they can control their operations, retrieve stolen data, and issue commands.
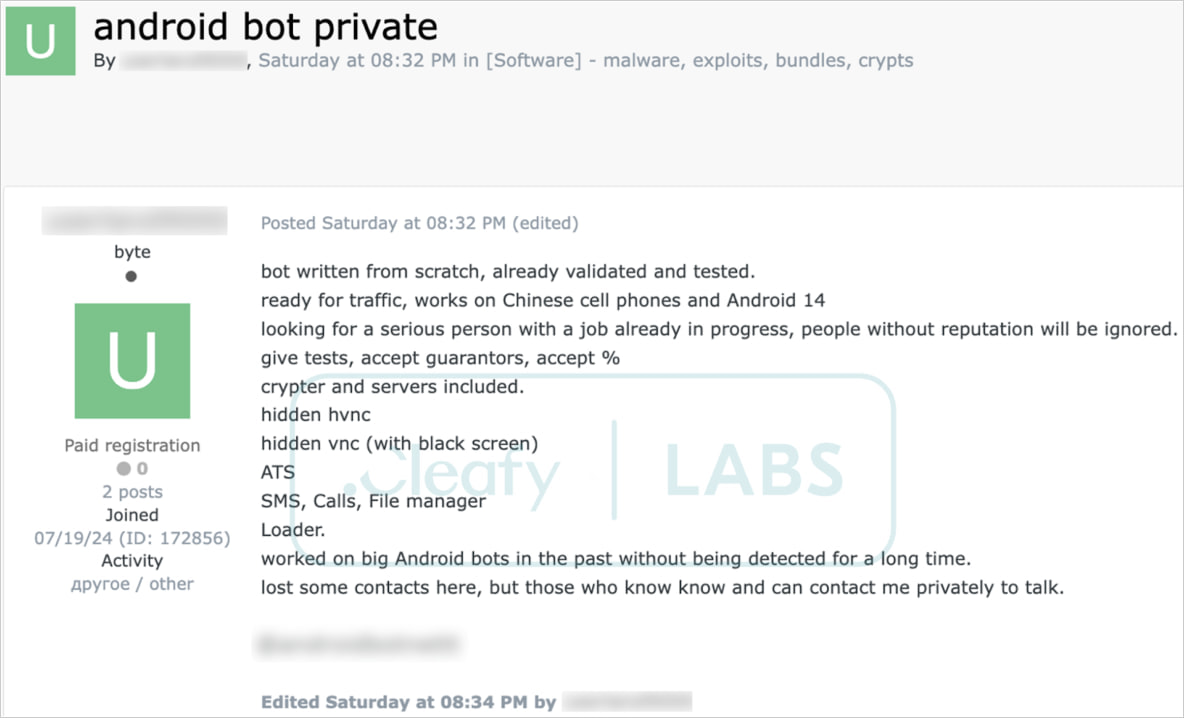 Creators claiming DroidBot works well on Android 14
Creators claiming DroidBot works well on Android 14Source: Cleafy
Multiple affiliates operate on the same C2 infrastructure, with unique identifiers assigned to each group, allowing Cleafy to identify 17 threat groups.
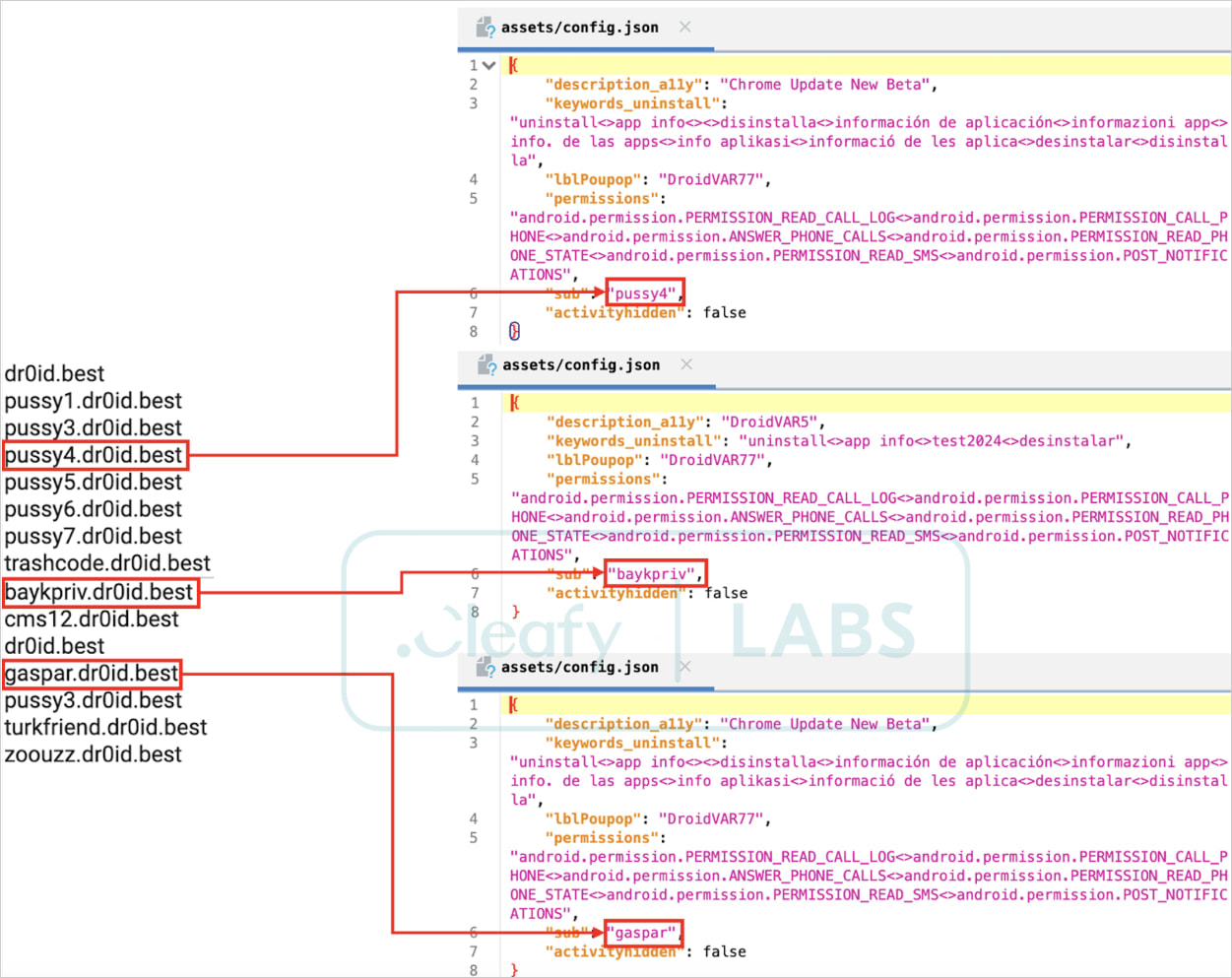 Affiliates extracted from the sample's configuration
Affiliates extracted from the sample's configurationSource: Cleafy
The payload builder allows the affiliates to customize DroidBot to target specific applications, use different languages, and set other C2 server addresses.
Affiliates are also provided access to detailed documentation, support from the malware's creators, and access to a Telegram channel where updates are published regularly.
All in all, the DroidBot MaaS operation makes the barrier of entry fairly low for inexperienced or low-skilled cybercriminals.
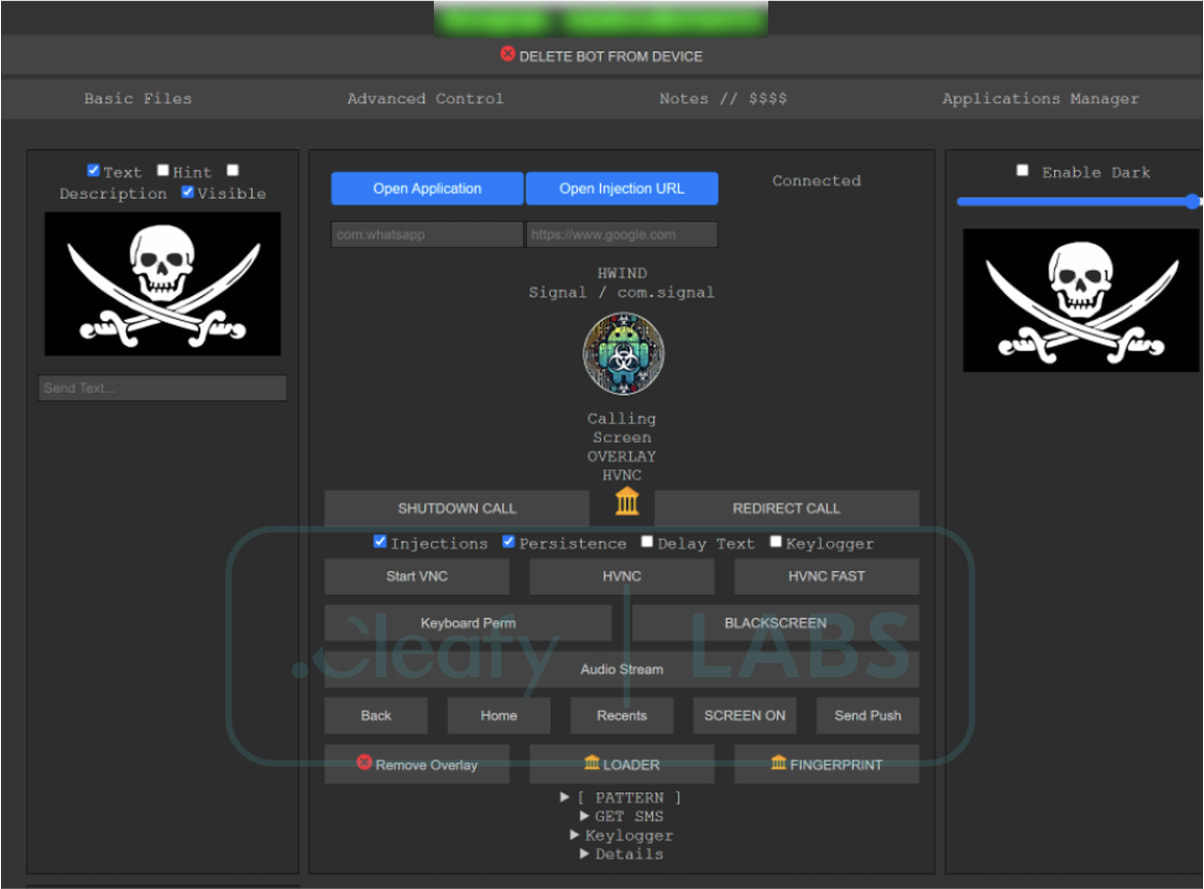 Admin panel giving affiliates complete control
Admin panel giving affiliates complete controlSource: Cleafy
Impersonating popular apps
DroidBot is often masqueraded as Google Chrome, Google Play store, or 'Android Security' as a way to trick users into installing the malicious app.
However, in all cases, it acts as a trojan attempting to steal sensitive information from apps.
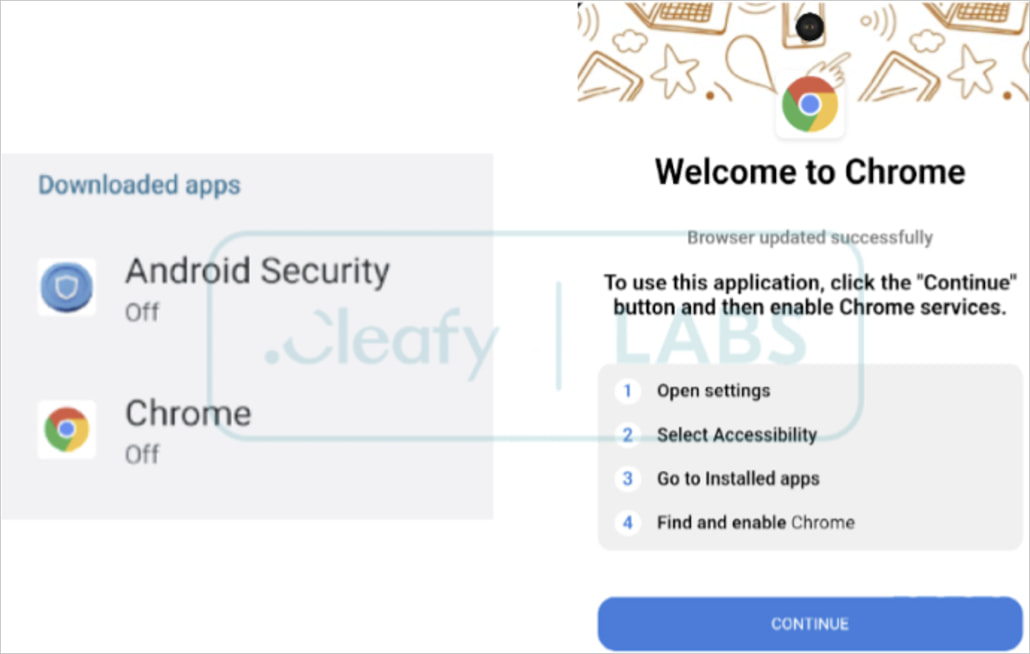 DroidBot's masking apps
DroidBot's masking appsSource: Cleafy
The main features of the malware are:
Keylogging – Capturing every keystroke entered by the victim. Overlaying – Displaying fake login pages over legitimate banking app interfaces. SMS interception – Hijacks incoming SMS messages, particularly those containing one-time passwords (OTPs) for banking sign-ins. Virtual Network Computing – VNC module gives affiliates the capability to remotely view and control the infected device, execute commands, and darken the screen to hide the malicious activity.A key aspect of DroidBot's operation is the abuse of Android's Accessibility Services to monitor user actions and simulate swipes and taps on behalf of the malware. Therefore, if you install an app that requests strange permissions, like the Accessibility Services, you should immediately become suspicious and deny the request.
Among the 77 apps DroidBot attempts to steal credentials, some standouts include Binance, KuCoin, BBVA, Unicredit, Santander, Metamask, BNP Paribas, Credit Agricole, Kraken, and Garanti BBVA.
To mitigate this threat, Android users are advised to only download apps from Google Play, scrutinize permission requests upon installation, and make sure Play Protect is active on their devices.
.png)















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·