Django Web application for performing Static Analysis and detecting malware in Android APKs
In each of the scans, it would have the following information:
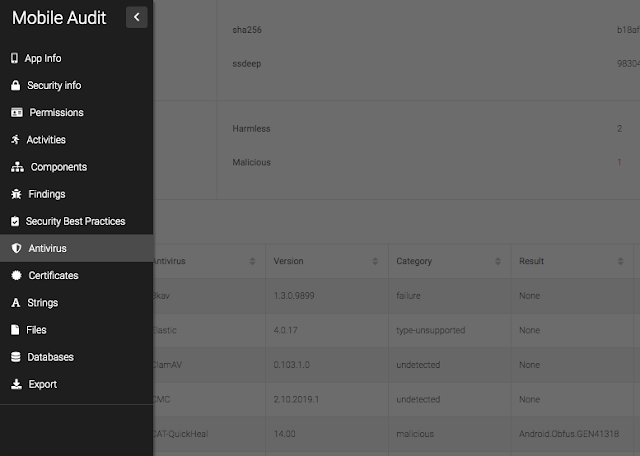
Application Info Security Info Components SAST Findings Best Practices Implemented Virus Total Info Certificate Info Strings Databases FilesFor easy access there is a sidebar on the left page of the scan:
Components
db: PostgreSQL 13.2 nginx: Nginx 1.19.10 rabbitmq: RabbitMQ 3.8.14 worker: Celery 5.0.5 web: Mobile Audit AppDocker Base images
Image is based on python buster. Link to Docker Hub image
| mpast/mobile_audit | 1.3.8 | python:3.9.4-buster |
| mpast/mobile_audit | 1.3.6 | python:3.9.2-buster |
| mpast/mobile_audit | 1.3.0 | python:3.9.1-buster |
| mpast/mobile_audit | 1.0.0 | python:3.9.0-buster |
Main features
Uses Docker for easy deployment in multiplatform environment Extract all information of the APK Analyze all the source code searching for weaknesses All findings are categorized and follows CWE standards All findings are categorized and include Mobile Top 10 Risk Also highlight the Best Practices in Secure Android Implementation in the APK The findings can be edited and the false positives can be triaged and deleted All scan results can be exported to PDF User authentication and user management API v1 with Swagger and ReDoc TLS Dynamic page reload (WIP) LDAP integration Export to Markdown Export to CSVPatterns
The application has an engine with different rules and patterns that are used though the findings scanning phase to detect vulnerabilities and/or malicious code into the apk.
These can be activated and deactivated in /patterns
Note: some of the hardcoded patterns are from apkleaks
Models
The application has an created models for each of the entities of the scans' information to be able to create relations an abtain the best conclusions for each of the apks.
To see the whole model schema, go to models
### Integrations
Virus Total (API v3)
It checks if there has been an scan of the APK and extract all its information. Also, there is the possibility of uploading the APK is selected a property in the environment (Disabled by default).
Defect Dojo (API v2)
It is possible to upload the findings to the defect manager.
MalwareDB & Maltrail
It checks in the database if there are URLs in the APK that are related with Malware.
Installation
Using Docker-compose:
The provided docker-compose.yml file allows you to run the app locally in development.
To build the local image and if there are changes to the local Application Dockerfile, you can build the image with:
Then, to start the container, run:
Optional: run in detached mode (not see the logs)
Once the application has launched, you can test the application by navigating to: http://localhost:8888/ to access the dashboard.
Also, there is a TLS version using docker-compose.prod.yaml running in port 443
To use it, execute
Then, you can test the application by navigating to: https://localhost/ to access the dashboard.
For more information, see TLS
To stop and remove the containers, run
API v1
REST API integration with Swagger and ReDoc.
Usage
Endpoint to authenticate and get token: /api/v1/auth-token/ Once authenticated, use header in all requests: Authorization: Token <ApiKey>Swagger
ReDoc
Endpoints
A JSON view of the API specification at /swagger.json A YAML view of the API specification at /swagger.yaml A swagger-ui view of the API specification at /swagger/ A ReDoc view of the API specification at /redoc/TLS
Pre-requirements
Add the certificates into nginx/ssl To generate a self-signed certificate:Nginx configuration
TLS - port 443: nginx/app_tls.conf Standard - port 8888: nginx/app.confDocker configuration
By default, there is a volume in docker-compose.yml with the configuration with 8888 available
** In production environment** use docker-compose.prod.yaml with port 443
Environment variables
All the environment variables are in a .env file, there is an .env.example with all the variables needed. Also there are collected in app/config/settings.py:
MALWARE_ENABLED = env('MALWARE_ENABLED', True)
MALWAREDB_URL = env('MALWAREDB_URL', 'https://www.malwaredomainlist.com/mdlcsv.php')
MALTRAILDB_URL = env('MALTRAILDB_URL', 'https://raw.githubusercontent.com/stamparm/aux/master/maltrail-malware-domains.txt')
VIRUSTOTAL_ENABLED = env('VIRUSTOTAL_ENABLED', False)
VIRUSTOTAL_URL = env('VIRUSTOTAL_URL', 'https://www.virustotal.com/')
VIRUSTOTAL_FILE_URL = env('VIRUSTOTAL_FILE_URL', 'https://www.virustotal.com/gui/file/')
VIRUSTOTAL_API_URL_V3 = env('VIRUSTOTAL_API_URL_V3', 'https://www.virustotal.com/api/v3/')
VIRUSTOTAL_URL_V2 = env('VIRUSTOTAL_API_URL_V2', 'https://www.virustotal.com/vtapi/v2/file/')
VIRUSTOTAL_API_KEY = env('VIRUSTOTAL_API_KEY', '')
VIRUSTOTAL_UPLOAD = env('VIRUSTOTAL_UPLOAD', False)
DEFECTDOJO_ENABLED = env('DEFECTDOJO_ENABLED', False)
DEFECTDOJO_URL = env('DEFECTDOJO_URL', 'http://defectdojo:8080/finding/')
DEFECTDOJO_API_URL = env('DEFECTDOJO_API_URL', 'http://defectdojo:8080/api/v2/')
DEFECTDOJO_API_KEY = env('DEFECTDOJO_API_KEY', '')
If you like to contribute, see Contributing
.png)
 3 years ago
248
3 years ago
248 

























 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·