Octopus is an open source, pre-operation C2 server based on python which can control an Octopus powershell agent through HTTP/S.
The main purpose of creating Octopus is for use before any red team operation, where rather than starting the engagement with your full operational arsenal and infrastructure, you can use Octopus first to attack the target and gather information before you start your actual red team operation.
Octopus works in a very simple way to execute commands and exchange information with the C2 over a well encrypted channel, which makes it inconspicuous and undetectable from almost every AV, endpoint protection, and network monitoring solution.
One cool feature in Octopus is called ESA, which stands for "Endpoint Situational Awareness", which will gather some important information about the target that will help you to gain better understanding of the target network endpoints that you will face during your operation, thus giving you a shot to customize your real operation based on this information.
Octopus is designed to be stealthy and covert while communicating with the C2, as it uses AES-256 by default for its encrypted channel between the powershell agent and the C2 server. You can also opt for using SSL/TLS by providing a valid certficate for your domain and configuring the Octopus C2 server to use it.
Octopus is packed with a number of features that allows you to gain an insight into your upcoming engagement before you actually need to deploy your full aresenal or tools and techniques, such as:
Control agents throught HTTP/S. Execute system commands. Download / Upload files. Load external powershell modules. Use encrypted channels (AES-256) between C2 and agents. Use inconspicuous techniques to execute commands and transfer results. Create custom and multiple listeners for each target. Generate different types of payloads. Support all windows versions with powershell 2.0 and higher. Run Octopus windows executable agent without touching powershell.exe process. Gather information automatically from the endpoint (endpoint situational awareness) feature.You can install all of Octopus' requirements via :
pip install -r requirements.txt
You need to install nasm for linux and 'mingw-w64' compiler to use the shellcoding feature and the spoofed args agent.
You can install nasm on Debian based distros using:
apt install nasm
And you can install mingw-w64 on Debian based distros using:
apt install mingw-w64
Octopus has been tested on the following operating systems:
Ubuntu (18.04) Ubuntu (16.04) Kali Linux (2019.2)You will also need to install mono to make sure that you can compile the C# source without issues.
Octopus depends on mono-csc binary to compile the C# source and you can install it by the following command apt install mono-devel which has been tested on kali and ubuntu 16.04.
you can use Octopus without installing mono but you will not be able to use generate_exe command.
Also please note that compling C# depends on the System.Management.Automation.dll assembly with SHA1 hash a43ed886b68c6ee913da85df9ad2064f1d81c470.
If you encounter any issues using Octopus, feel free to file a bug report!
First of all make sure to download the latest version of Octopus using the following command :
git clone https://github.com/mhaskar/Octopus/
Then you need to install the requirements using the following command :
pip install -r requirements.txt
After that you can start the octopus server by running the following :
./octopus.py
You will by greeted with the following once you run it :
Using Octopus is quite simple to use, as you just need to start a listener and generate your agent based on that listener's information.
You can generate as many listeners as you need, and then you can start interacting with your agents that connect to them.
Profile setup
Before you can start using Octopus you have to setup a URL handling profile which will control the C2 behavior and functions, as Octopus is an HTTP based C2 thus it depends on URLs to handle the connections and to guarantee that the URLs will not serve as a signatures or IoC in the network you are currently attacking, the URLs can be easily customized and renamed as needed.
Profile setup currently only support URL handling, auto kill value and headers.
Setting up your profile
To start setting up your profile you need to edit the profile.py file , which contains a number of key variables, which are:
file_reciever_url: handles file downloading. report_url: handle ESA reports. command_send_url: handles the commands that will be sent to the target. command_receiver_url: handles commands will be executed on the target. first_ping_url: handles the first connection from the target. server_response_header: this header will show in every response. auto_kill: variable to control when the agent will be killed after N failed connections with the C2Example:
The agent and the listeners will be configured to use this profile to communicate with each other. Next we need to know how to create a listener.
Listeners
Octopus has two main listeners,"http listener" and "https listener" , and the options of the two listeners are mostly identical.
HTTP listener :
listen_http command takes the following arguments to start:
BindIP Defines the IP address that will be used by the listener. BindPort Defines the port you want to listen on. Hostname Will be used to request the payload from. Interval How number of seconds the agent will wait before checking for commands. URL The name of the page hosting the payload. Listener_name Listener name to use.you can also view an example of it by running the listen_http command:
And we can start a listener using the following command :
listen_http 0.0.0.0 8080 192.168.178.1 5 page.php operation1
The following result will be returned:
a listener has been started successfully, and we can view all the listeners using the listeners command:
HTTPS listener :
To create an HTTPS listener you can use listen_https command as such:
The listen_https command takes the following arguments to start:
BindIP : which is the IP address that will be used by the listener BindPort : which is the port you want to listen on Hostname : will be used to request the payload from Interval : how may seconds that agent will wait before check for commands URL page : name will hold the payload Listener_name : listener name to use certficate_path : path for valid ssl certficate (called fullchain.pem for letsencrypt certficates) key_path : path for valid key for the ssl cerficate (called key.pem for letsencrypt certficates)Please note that you need to provide a valid SSL certficate that is associated with the domain used.
Generate agents
Powershell oneliner
To generate an agent for the listener operation1 we can use the following command:
generate_powershell operation1
and we will get the following result:
Now we can use this oneliner to start our agent.
HTA oneliner
To generate a HTA oneliner for the listener1 operation1 we can use the following command:
generate_hta operation1
and we will get the following results:
Please note that you can edit the /hta URL using profile.py
Octopus EXE agent
To generate an EXE agent for listener operation1 we can use the following command:
generate_unmanaged_exe operation1 /opt/Octopus/file.exe
and we will get the following result:
Please note that you have to install mono-csc to compile the C# source.
Octopus Spoofed arguments agent
You can generate a new EXE agent that will run a Powershell process with spoofed arguments based on Adam Chester's brilliant research.
To generate this exe, you can use the following command:
Generate x64 shellcode and x86 shellcode
Octopus can generate both x64 and x86 shellcode starting from version 1.2, the generated shellcode is using CreateProcessA to start powershell.exe oneliner that will launch powershell agent.
To generate x64 shellcode, you can use the following command:
To generate x86 shellcode, you can use the following command:
Interacting with agents
First of all you can list all connected agents using the list command to get the following results:
And then we can use the interact command to interact with the host as follows:
You can list all the available commands using the help command like the following:
To execute a system command directly we can type the command directly and then wait for the results based on the interval check time that we set when we created the listener.
In this case the command has been encrypted and then sent to the agent, after that the client will decrypt the command and execute it, the agent will encrypt the results, and finally send it back again to the C2 to decrypt it and show the results.
We can also use the report command to get the ESA information like the following:
You can load an external powershell module by placing it in the modules directory, then executing load module.ps1.
Also you can list all of the modules in the modules directory by executing the modules command like so:
Octopus v1.0 stable: Cobalt Strike deployment & much more!
Unveiling Octopus: The pre-operation C2 for Red Teamers
Ian Lyte for reporting multiple bugs in Octopus and pushing an enhanced AMSI bypass module.
Khlief for adding HTA module and fix a bug in download feature
Moath Maharmah for enhancing the encryption module and writing a standalone C# Octopus agent which will be added to the upcoming release.
TeslaPulse for testing Octopus
J005 for adding enhanced Powershell oneliner and fix an issue in the HID attack script.
This project is licensed under the GPL-3.0 License - see the LICENSE file for details
.png)
 2 years ago
165
2 years ago
165 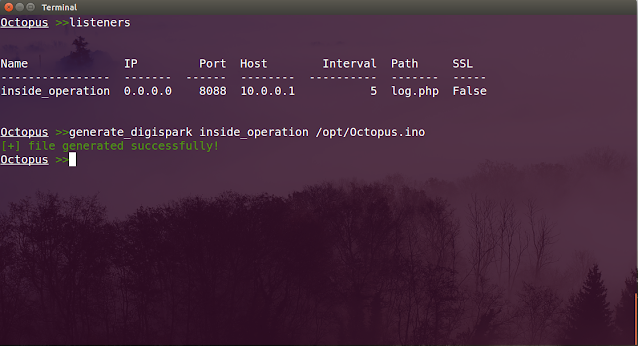
















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·