BOOK THIS SPACE FOR AD
ARTICLE AD
With PERI Finance dApp launching around the corner, we are starting a Bug Bounty Program to find bugs in our dApp. PERI Finance understands that blockchain and dApps are all about security thus we encourage anyone to join our bug bounty program. We have had several rounds of internal tests and working with external audit firms, but nothing guarantees total security so it is crucial to get as many tests as we can before the main deployment.
PERI Finance bug bounty program will hold with Immunefi. Participants can submit at Immunefi PERI Page and the final decision of the reward, which is affected by the exploitability of the bug report, is done by PERI Finance.
(Payouts are handled by the PERI Finance team directly and are denominated in USD. Payouts are done in USDT.)
We are offering 4 levels of bug bounties where rewards are distributed according to the impact of the vulnerability based on the Immunefi Vulnerability Severity Classification System.
[Assets in Scope]
[Rules and Disclaimer]
Rewards will be decided on a per case basis. This bug bounty program’s terms and conditions are at the sole discretion of PERI Finance.Rewards will vary depending on the severity of the issue.The bugs being considered for the reward are based on first come first serve basis, duplicate bugs will not be considered.Can edit or provide more information. Do not create a new submission.Determinations of eligibility, score and all terms related to an award are the sole and final discretion of PERI Finance.žKYC Required for the participantsThe Following activities are prohibited by bug bounty program:
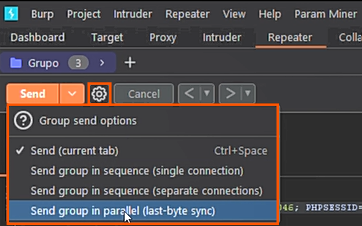
žAny testing with mainnet or public testnet contracts; all testing should be done on private testnets.Any testing with pricing oracles or third party smart contracts.Attempting phishing or other social engineering attacks against our employees and/or customers.Any testing with third party systems and applications (e.g. browser extensions) as well as websites (e.g. SSO providers, advertising networks)Any denial-of-service attacks.žAutomated testing of services that generates significant amounts of traffic.Public disclosure of an unpatched vulnerability in an embargoed bounty..png)
 3 years ago
196
3 years ago
196 











 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·