Scans web applications for second-order subdomain takeover by crawling the app, and collecting URLs (and other data) that match certain rules, or respond in a certain way.
Installation
From binary
Download a prebuilt binary from the releases page and unzip it.
From source
Go version 1.17 is recommended.
Docker
Command line options
Directory to save results in (default "output") -threads int Number of threads (default 10)">
-target stringTarget URL
-config string
Configuration file (default "config.json")
-depth int
Depth to crawl (default 1)
-header value
Header name and value separated by a colon 'Name: Value' (can be used more than once)
-insecure
Accept untrusted SSL/TLS certificates
-output string
Directory to save results in (default "output")
-threads int
Number of threads (default 10)
Configuration File
Example configuration files are in config
LogQueries: A map of tag-attribute queries that will be searched for in crawled pages. For example, "a": "href" means log every href attribute of every a tag. LogNon200Queries: A map of tag-attribute queries that will be searched for in crawled pages, and logged only if they contain a valid URL that doesn't return a 200 status code. LogInline: A list of tags whose inline content (between the opening and closing tags) will be logged, like title and scriptOutput
All results are saved in JSON files that specify what and where data was found
The results of LogQueries are saved in attributes.json"https://example.com/": {
"input[name]": [
"user",
"id",
"debug"
]
}
}
"https://example.com/": {
"script[src]": [
"https://cdn.old_abandoned_domain.com/app.js",
]
}
}
"https://example.com/": {
"title": [
"Example - Home"
]
},
"https://example.com/login": {
"title": [
"Example - login"
]
}
}
Usage Ideas
This is a list of tips and ideas (not necessarily related to second-order subdomain takeover) on what to use Second Order for.
Check for second-order subdomain takeover: takeover.json. (Duh!) Collect inline and imported JS code: javascript.json. Find where a target hosts static files cdn.json. (S3 buckets, anyone?) Collect <input> names to build a tailored parameter bruteforcing wordlist: parameters.json. Feel free to contribute more ideas!References
https://shubs.io/high-frequency-security-bug-hunting-120-days-120-bugs/#secondorder
.png)
 2 years ago
138
2 years ago
138 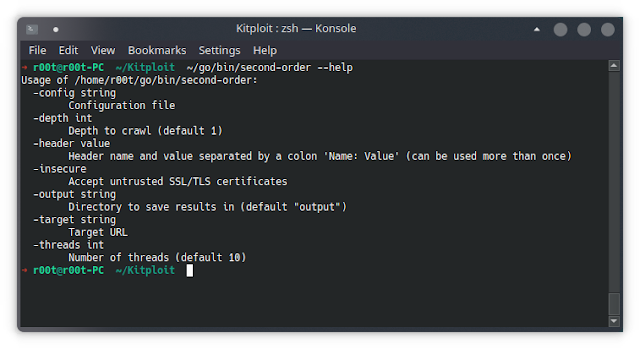
















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·