BOOK THIS SPACE FOR AD
ARTICLE ADA new info-stealing malware called Bandit Stealer is capable of evading detection and stealing personal and financial banking data stored in cryptocurrency wallets and web browsers.
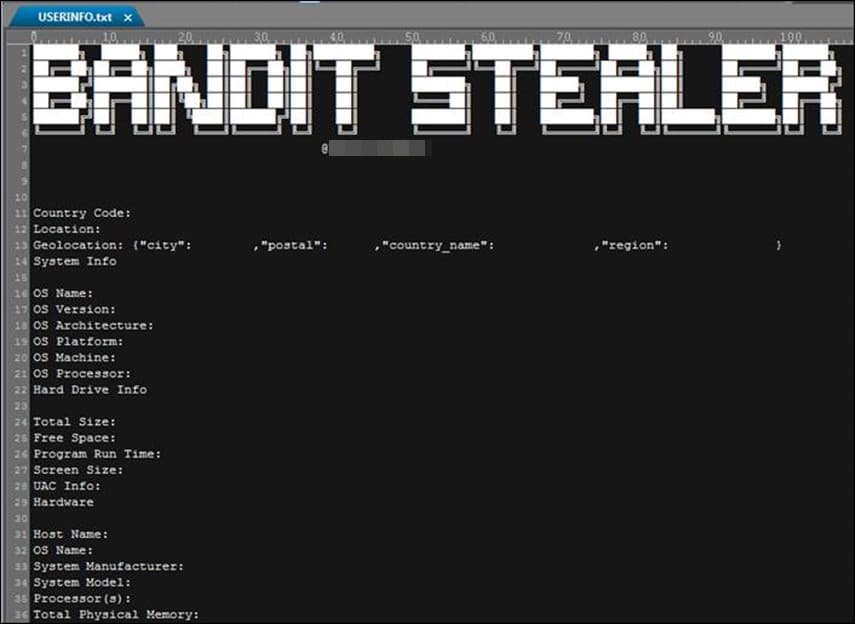
Bandit Stealer is a new information stealer that Trend Micro cybersecurity researchers recently detected. According to their analysis, Bandit Stealer can target cryptocurrency wallets and web browsers and successfully evade detection.
Currently, Bandit Stealer is targeting Windows devices, but the malware has the potential to extend its reach to other platforms as well since it is developed using the Go programming language, which means it has cross-platform compatibility. It can check whether it is running in a virtual environment or sandbox and quickly terminate blocklisted processes to evade detection on the compromised system.
It is worth noting that the malware is distributed through phishing emails. These emails contain a dropper file, which launches a harmless-looking MS Word attachment to distract the user. In the background, it triggers the infection chain.
The malware targets Windows by using a legitimate command-line tool known as runas.exe. This tool allows users to run programs for a different purpose with different permissions. The primary objective is to gain privilege escalation and execute the file with administrative access to bypass security mechanisms and steal a wider range of data.
“By using the runas.exe command, users can run programs as an administrator or any other user account with appropriate privileges, provide a more secure environment for running critical applications, or perform system-level tasks,” Trend Micro researchers wrote in a blog post.
It is worth noting that Microsoft’s access control prevention mechanism will require it to run the malware binary as an administrator after receiving the necessary credentials. This utility is useful when the current user account doesn’t offer sufficient privilege for executing a specific program command.
The malware establishes persistence through Windows Registry modifications and collects data, including personal and financial banking data stored in crypto wallets and web browsers.
Researchers claim to have discovered a fake installer of the Heart Sender service, which is used to automate the spam SMS and email sending process. Through this trick, the user unknowingly launches the embedded malware.
Attackers can use the information stolen through Bandit Stealer and other stealers in various ways. They can exploit it for identity theft, data breaches, financial gain, account hijacking, and credential-stuffing campaigns. They can also sell it to other cybercriminals or use it in follow-on attacks, such as double extortion and ransomware attacks.
.png)















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·