A tool for UEFI firmware reverse engineering.
UEFI firmware analysis with uefi_retool.py script
Usage:
get-images
python uefi_retool.py get-images --help
Usage: uefi_retool.py get-images [OPTIONS] FIRMWARE_PATH
Get executable images from UEFI firmware. Images are stored in "modules"
directory.
Options:
--help Show this message and exit.Example:
python uefi_retool.py get-images test_fw/fw-tp-x1-carbon-5th.bin
get-info
python uefi_retool.py get-info --help
Usage: uefi_retool.py get-info [OPTIONS] FIRMWARE_PATH
Analyze the entire UEFI firmware. The analysis result is saved to .json
file.
Options:
-w, --workers INTEGER Number of workers (8 by default).
--help Show this message and exit.Example:
python uefi_retool.py get-info -w 6 test_fw/fw-tp-x1-carbon-5th.bin
get-pp
python uefi_retool.py get-pp --help
Usage: uefi_retool.py get-pp [OPTIONS] FIRMWARE_PATH
Get a list of proprietary protocols in the UEFI firmware. The result is
saved to .json file.
Options:
-w, --workers INTEGER Number of workers (8 by default).
--help Show this message and exit.Example:
python uefi_retool.py get-pp -w 6 test_fw/fw-tp-x1-carbon-5th.bin
Additional tools
tools/update_edk2_guids.py is a script that updates protocol GUIDs list from edk2 projectIDA plugin
IDA plugin for UEFI analysis
Analyser & Protocol explorer
Usage
Copy uefi_analyser and uefi_analyser.py to your %IDA_DIR%/plugins directoryOpen the executable UEFI image in IDA and go to Edit -> Plugins -> UEFI analyser (alternatively, you can use the key combination Ctrl+Alt+U)
Example
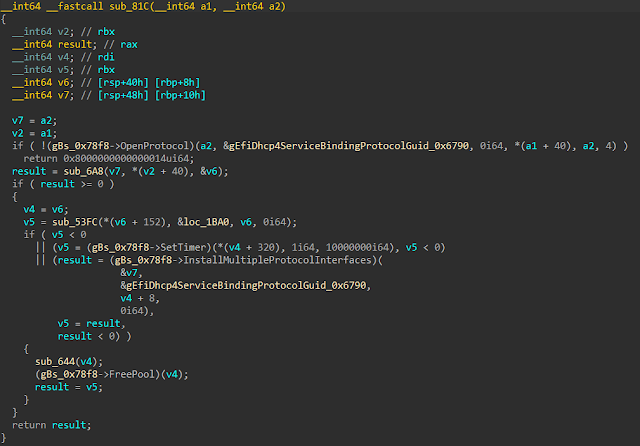
Before analysis
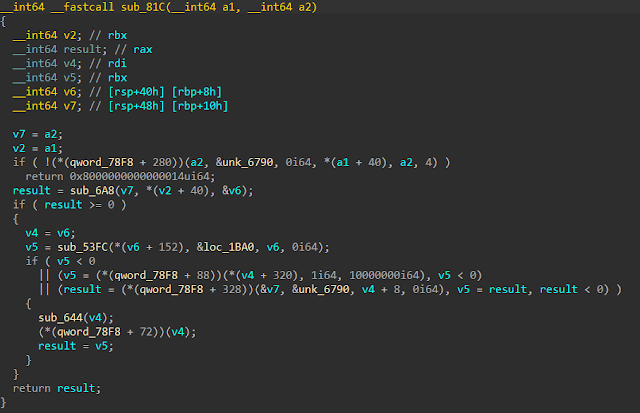
After analysis
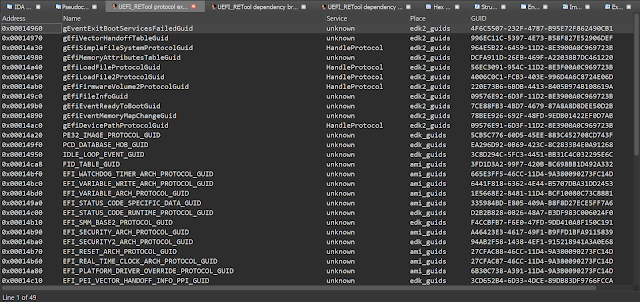
Protocol explorer window
Dependency browser & Dependency graph
Usage
Analyse the firmware using uefi_retool.py
python uefi_retool.py get-info FIRMWARE_PATH
Load <LOGS_DIR>/<FIRMWARE_NAME>-all-info.json file to IDA (File -> UEFI_RETool...)
alternatively, you can use the key combination Ctrl+Alt+J)
Example
Dependency browser window
Dependency graph
Similar works
ida-efiutils EFISwissKnife ghidra-firmware-utils.png)
 4 years ago
226
4 years ago
226 


















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·